Introduction
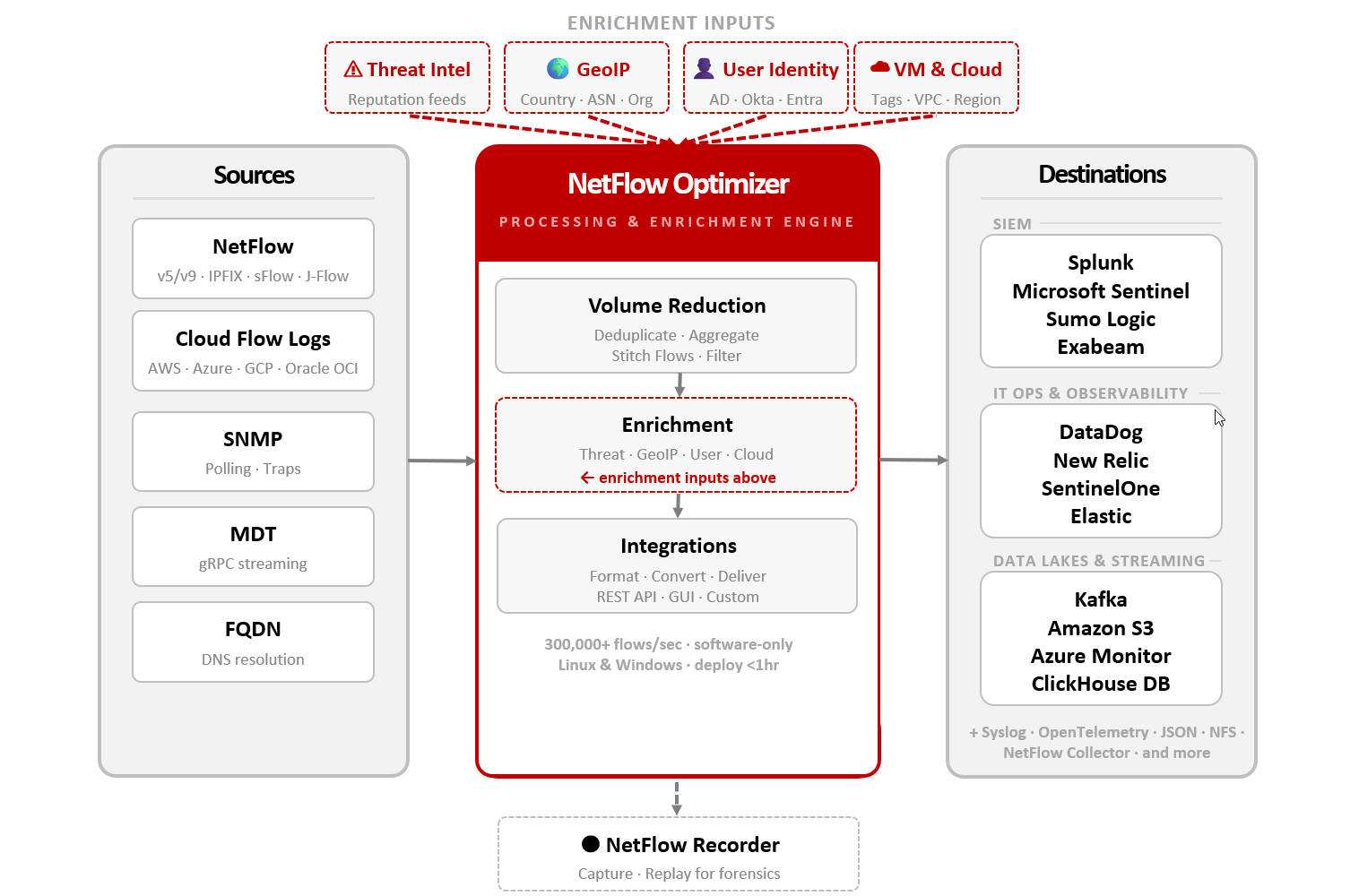
NetFlow Optimizer™ (NFO) is a high-performance, software-only processing engine that transforms massive streams of raw network data into high-fidelity, actionable intelligence — before it reaches your SIEM, IT operations platform, or data lake.
NFO acts as a vendor-agnostic pre-processor. It ingests data from physical, virtual, and cloud environments, reduces volume, enriches records with business context, and delivers a clean, optimized stream to your downstream systems in real time.
What NFO Does
NetFlow Optimizer provides a 360-degree view of your network by unifying two critical data streams:
- Flow Optimization & Enrichment: NFO accepts NetFlow, IPFIX, sFlow, and J-Flow from network hardware, alongside Cloud Flow Logs from AWS, Azure, OCI, and Google VPC. It deduplicates, aggregates, and enriches these records so your SIEM receives only high-value, context-rich data.
- Infrastructure Metrics: NFO actively polls devices via SNMP and Model-Driven Telemetry (MDT) for performance metrics, and receives SNMP Traps for immediate event notification.
Core Capabilities
Volume Reduction
Modern networks generate a "NetFlow Tsunami" that can overwhelm SIEM storage and inflate licensing costs. NFO intelligently reduces data volume by 80–90% without sacrificing the visibility required for security and compliance.
- Intelligent Aggregation: Summarizes similar flows and optionally excludes ephemeral client ports, collapsing hundreds of micro-flows into a single high-value record.
- Deduplication: Identifies and removes redundant flow records caused by overlapping collection points, ensuring only unique information is forwarded.
- Flow Stitching: Reconstructs unidirectional flows into complete bidirectional conversations, providing a 360-degree view of interactions while reducing record counts by an additional 50%.
- Top N Analysis: Automatically surfaces the most impactful traffic patterns — top talkers, heaviest bandwidth consumers, and most-used applications.
Context Enrichment
Raw IP addresses are "naked" data — they show how much, but not who or why. NFO transforms connection records into rich, context-aware intelligence ready for security analysis and AI/ML pipelines.
- User Identity: Links traffic to specific users via Active Directory, Okta, and Microsoft Entra ID.
- Threat Intelligence: Automatically flags communications with known malicious actors using real-time threat reputation feeds.
- GeoIP & Location: Maps every flow to a physical location, country, and ASN using industry-standard geolocation databases.
- Cloud & VM Context: Correlates flows with VM names and cloud instance metadata (AWS/Azure/GCP/OCI) to simplify investigations in hybrid environments.
- Format Normalization: Converts disparate telemetry — NetFlow v5/v9, IPFIX, sFlow, Cisco ASA, and cloud VPC flow logs — into standardized, CIM-compliant (Splunk) records, so your dashboards and detection rules work consistently regardless of hardware vendor.
Investment Leveraging
NFO is designed to extend and maximize the tools you already have — not replace them.
- Native SIEM Integration: Streams enriched data directly into Splunk, Microsoft Sentinel, CrowdStrike, Sumo Logic, Exabeam, and more.
- IT Ops & Observability: Feeds DataDog, New Relic, Elastic, and other monitoring platforms with the same optimized stream.
- Data Lakes & Streaming: Delivers to Kafka, Amazon S3, Azure Monitor, ClickHouse, and OpenSearch for long-term retention and analytics.
- Cost Management: By reducing volume before data reaches downstream platforms, NFO dramatically lowers ingestion and storage costs — allowing you to monitor more network for the same budget.
Multi-Group Infrastructure Insights: Autonomous Classification
Traditional SNMP monitoring often requires manual configuration for every new device, leading to visibility gaps and configuration drift. NetFlow Optimizer (NFO) eliminates the manual burden of mapping thousands of Object Identifiers (OIDs) through its Autonomous Classification Engine. This model automates infrastructure discovery and classification from day one.
Instead of manual templates, NFO uses a Multi-Group Inheritance model to ensure every device in your estate is monitored accurately and immediately.
- Zero-Touch Discovery: As new hardware is added, NFO automatically detects the vendor, role, and feature set. It identifies the hardware and tags it by role (e.g., Firewall, Switch, or Router) without requiring manual intervention.
- Hierarchical Inheritance: Devices inherit monitoring profiles based on their position in the infrastructure hierarchy. A switch identified as "Cisco + Core + Layer 3" instantly receives the correct polling intervals and vendor-specific OID maps.
- Contextual Health Mapping: Role-specific metrics ensure that critical infrastructure is monitored with the appropriate urgency. For example, a congested interface on a backbone trunk is prioritized and analyzed differently than one on a standard access port.
- Dynamic Inventory Tracking: NFO maintains a real-time, self-updating inventory of your entire estate. It continuously audits software versions and device features, simplifying compliance reporting and lifecycle management.
Summary of Value
| Capability | Problem Solved | Business Outcome |
|---|---|---|
| Volume Reduction | NetFlow Tsunami | Up to 90% reduction in SIEM storage and licensing costs |
| Enrichment | "Naked" IP context | Instant user and threat attribution — zero manual lookups |
| Investment Leveraging | Tool silos | Maximized ROI from existing SIEM and IT Ops platforms |
| Multi-Group Insights | Manual configuration | Zero-touch device onboarding and 100% estate visibility |
Next Steps
- Get Started with NFO: Install and configure NFO in under an hour
- Flow Sources: Supported protocols and cloud flow log formats
- Destinations: Configure output to your SIEM, IT Ops, or data lake platform
- Enrichment: Set up user identity, GeoIP, and threat intelligence feeds
- SNMP Monitoring: Enable device discovery and infrastructure metrics