Introduction
The NetFlow Logic team is pleased to announce the availability of NetFlow-based DDoS Detection solution. This solution brings new anomalous traffic detection capabilities to businesses by providing early detection of DDoS attack before network devices and servers targeted by DDoS are incapacitated.
DDoS attacks are notoriously difficult to detect timely and defend against. Traditional perimeter based technologies such as firewalls and intrusion detection systems (IDSs) do not provide comprehensive DDoS protection. Solutions positioned inline must be deployed at each endpoint, and are vulnerable in case of a volumetric attack. Typically, solutions require systems to run in "learning" mode, passively monitoring traffic patterns to understand normal behavior and establish a baseline profile. The baseline is later used to detect anomalous network activity, which could be a DDoS attack. These takes a long time to implement and any change in the infrastructure makes baseline obsolete, and results in lots of false positives.
In contrast to the inline solutions, NetFlow Logic’s DDoS Detector solution is based on the flow information analysis, thus it is not susceptible to volumetric flood attacks. Also, it does not rely on baseline data collection, which may take days or weeks. Instead, NetFlow Logic’s anomalous traffic detection solution uses an innovative approach which makes it operational in 15-20 minutes after deployment.
NetFlow Logic’s solution is based on advanced statistical and machine learning methods and consists of several components each analyzing network metadata from a different perspective. Results of the analysis are combined and a final event reporting decision is made. The objective of such “collective mind” approach is false positives reduction.
The core of NetFlow Logic’s solution is NetFlow Optimizer™ (NFO) and DDoS Detector NFO Module.
NFO is a processing engine for network flow data (NetFlow, IPFIX, sFlow, etc.). It is not a NetFlow collector.
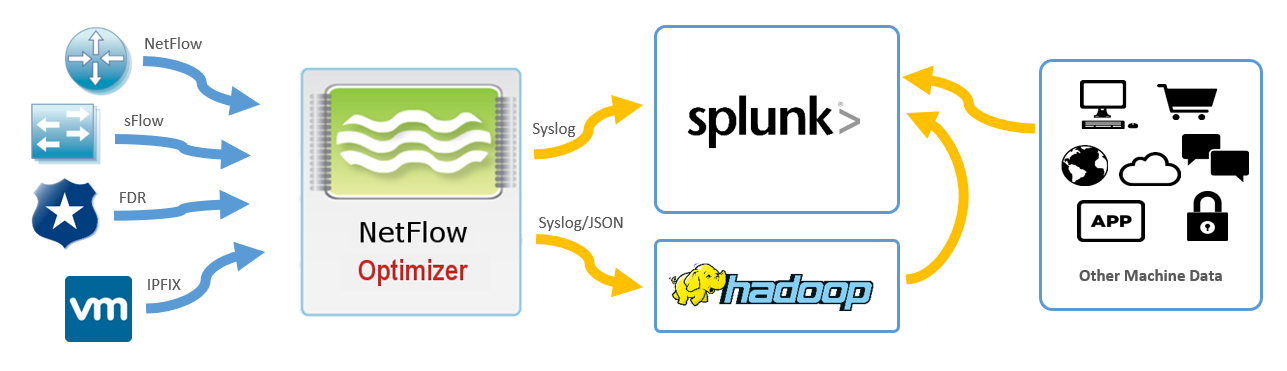
NetFlow Optimizer accepts network flow data from network devices (routers, switches, firewalls), applies analytical algorithms to the data to address various use cases, converts the processed data to a desired format such as syslog or JSON, then sends that processed information to other systems such as 3rd party DDoS mitigation service, or SIEM (e.g. VMware vRealize Log Insight, VMware vRealize Operations, or Splunk Enterprise).