The Analytical Engine: Meet the Experts
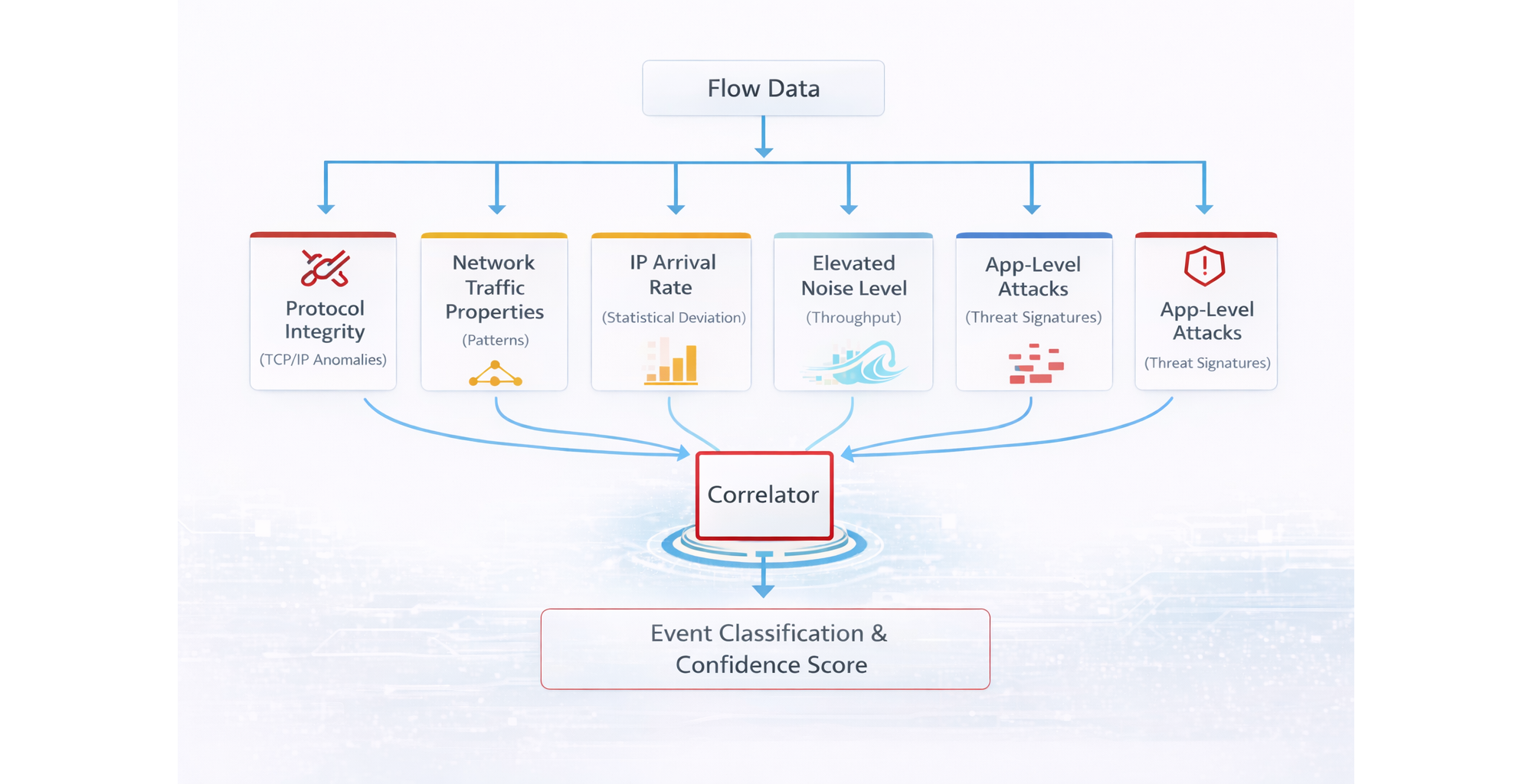
At the core of the NFO DDoS Detection Solution is a sophisticated multi-engine architecture known as the "Collective Mind." Rather than relying on a single, easily fooled bandwidth threshold, NFO utilizes a parallel processing framework where multiple specialized "Experts" analyze the flow data simultaneously. Their individual findings are then synthesized by a central Correlator to produce high-fidelity security intelligence.
The Six Analytical Experts
To ensure 90% fewer false positives, every flow record is processed through six specialized engines:
1. Expert A: TCP/IP Information
This engine monitors protocol-level data to identify malformed handshakes, header anomalies, and broken connection states. It specifically flags inconsistencies in TCP flags that indicate an attacker is attempting to exploit the underlying network stack.
2. Expert B: Network Traffic Properties
This expert inspects the fundamental characteristics and metadata of the traffic stream to identify deviations from standard communication norms. By analyzing packet sizes and flow durations, it can distinguish between legitimate high-bandwidth applications and malicious traffic spikes.
3. Expert C: New IP Address Arrival Rate
This module specifically detects spikes in the velocity of unique, previously unseen IP addresses entering the network. A rapid influx of new source IPs is a primary indicator of botnet activity and distributed volumetric attacks.
4. Expert D: Network Noise Level
This engine identifies elevated background "noise" and suspicious reconnaissance patterns that often precede or mask a coordinated attack. It effectively filters out "internet background radiation" so the SOC can focus on targeted threats.
5. Expert E: Application Layer Attacks
This expert focuses on Layer 7 threats that target specific services, such as HTTP, DNS, or SIP, rather than just overwhelming network bandwidth. It recognizes sophisticated patterns that mimic real user behavior while attempting to exhaust application resources.
6. Expert F: Low and Slow Attacks
This engine detects stealthy threats that use small amounts of traffic over long durations to keep connections open and exhaust server resources. By monitoring session persistence, it catches attacks that stay below the thresholds of traditional volume-based alarms.
The Correlation Hub
The individual outputs from all six experts converge at the Correlator. This central hub performs Events Correlation, comparing the different perspectives of each expert to distinguish between legitimate traffic surges and actual malicious activity.
By cross-referencing these six distinct data points, the Correlator provides a final output consisting of:
- Event Classification: A clear identification of the specific attack type.
- Confidence Score: A probability rating that helps your SOC prioritize response efforts.
Key Differentiator: Multi-Dimensional Accuracy
Because NFO uses this "Collective Mind" approach, it does not suffer from the "blind spots" of single-algorithm detectors. Even if an attacker attempts to hide a volumetric flood within a "low and slow" protocol attack, the combination of Expert C (Arrival Rate) and Expert F (Low and Slow) ensures the threat is identified and classified with a high confidence score.
Key Differentiators: Multi-Dimensional Accuracy and Rapid Protection
Because NFO uses this "Collective Mind" approach, it does not suffer from the "blind spots" of single-algorithm detectors. Even if an attacker attempts to hide a volumetric flood within a "low and slow" protocol attack, the combination of Expert C (Arrival Rate) and Expert F (Low and Slow) ensures the threat is identified and classified with a high confidence score.
Beyond its analytical depth, the solution provides the critical advantage of requiring no long-term baselining. Unlike traditional solutions that require weeks of "learning mode" to establish a traffic profile, NFO identifies attacks based on real-time statistical and protocol anomalies. This ensures the system is typically operational and providing protection within 15 minutes of deployment, offering immediate defense without the wait for historical data collection.