Sentinel Workbooks Reference
NetFlow Optimizer (NFO) provides pre-configured Microsoft Sentinel Workbooks that deliver immediate visibility into your network’s security and performance. By utilizing the enriched data pushed from NFO, these dashboards allow your SOC team to move beyond simple log searching to proactive, visual threat hunting.
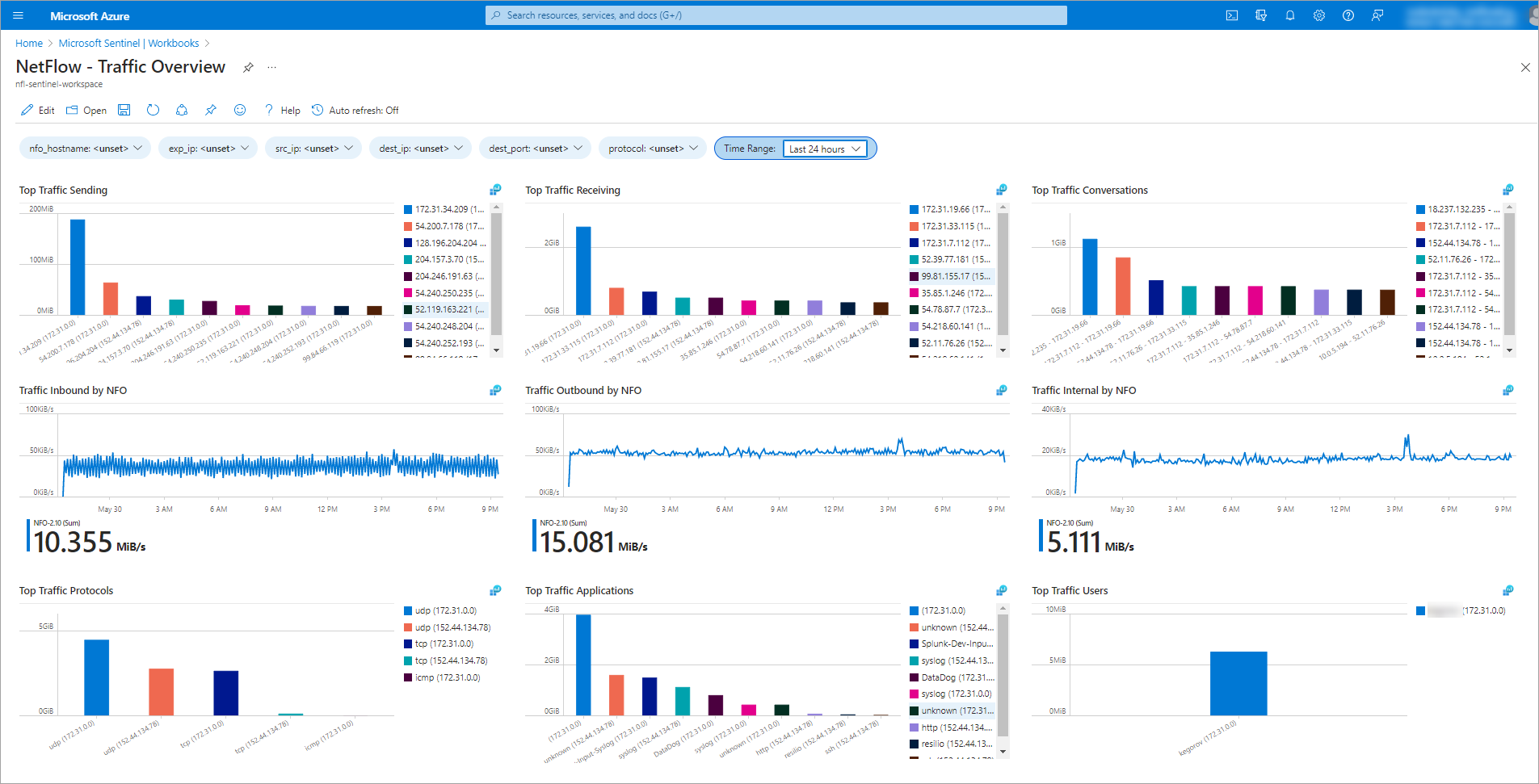
1. Traffic Overview
This workbook is designed to monitor network traffic by volume and host, providing a high-level view of your environmental health. It is the primary tool for identifying "Top Talkers" and understanding bandwidth distribution across your infrastructure.
Key Insights:
- Top Traffic Sending & Receiving: Identify the most active hosts on your network.
- Protocol & Application Breakdown: See which protocols (TCP, UDP, ICMP) and applications are consuming the most bandwidth.
- Inbound/Outbound Trends: Monitor traffic directionality and volume over time.
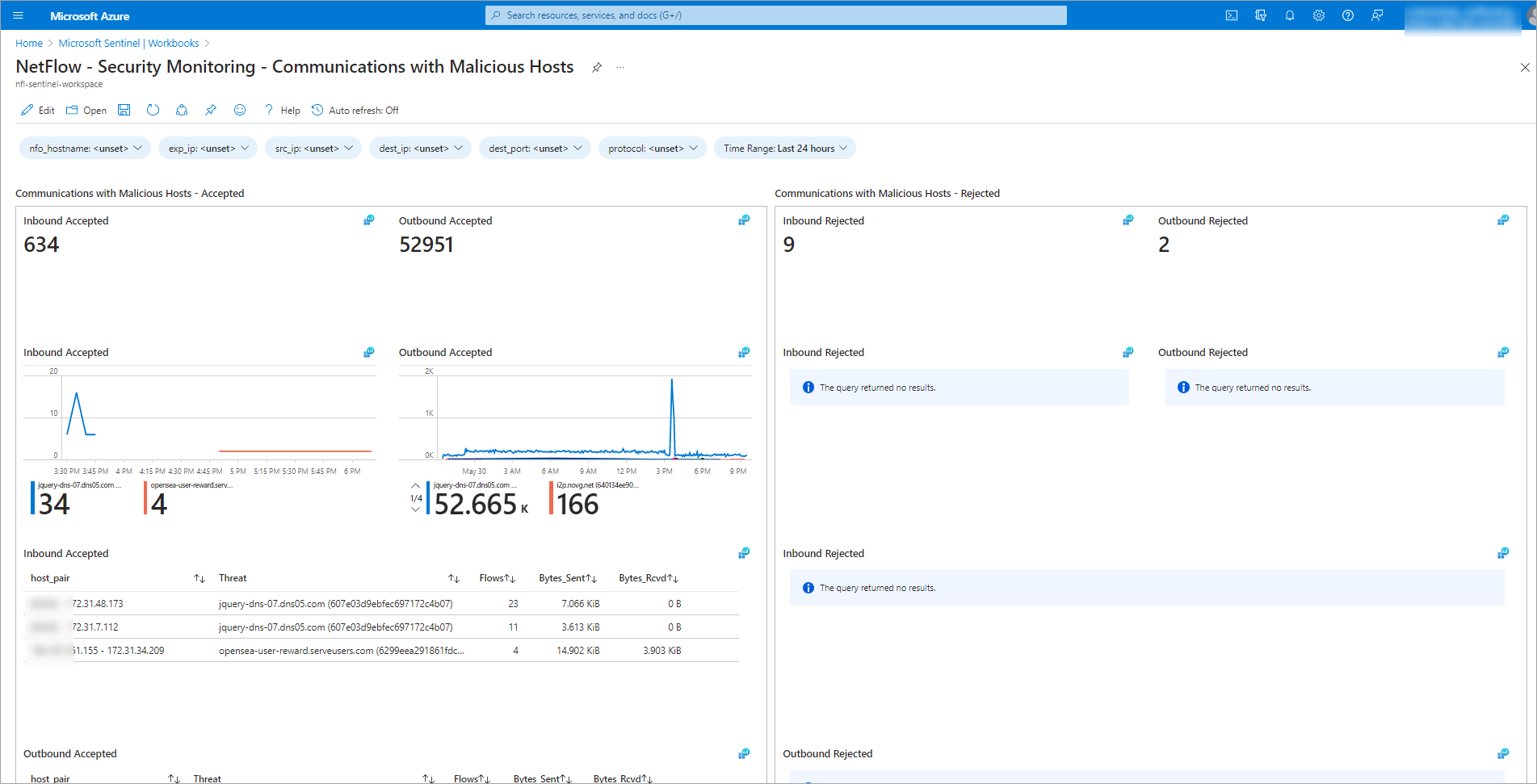
2. Security Monitoring: Communications with Malicious Hosts
This workbook focuses on threat detection by categorizing network traffic based on threat feed and reputation. It allows security analysts to immediately see if internal assets are communicating with known bad actors.
Key Insights:
- Threat Categorization: View threats organized by specific reputation scores and intelligence feeds.
- Accepted vs. Rejected Traffic: Distinguish between blocked connection attempts and successful communications with malicious entities.
- Affected Host Tracking: List specific internal hosts that have been flagged for high-risk communications.
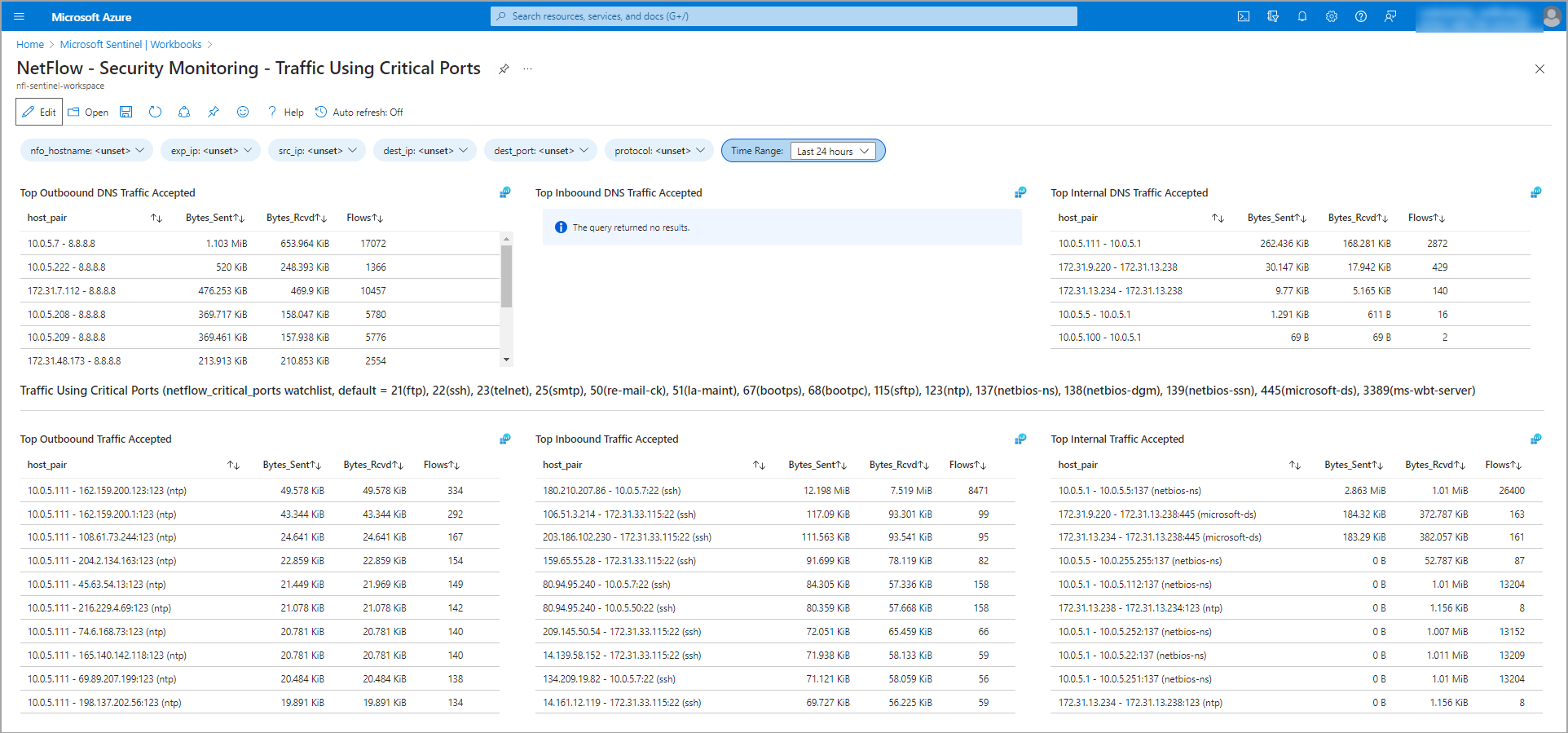
3. Security Monitoring: Traffic Using Critical Ports
This workbook provides specialized analytics for DNS traffic and the usage of critical network ports. It is essential for auditing compliance and detecting unauthorized use of high-risk services.
Key Insights:
- DNS Analytics: Monitor top internal and outbound DNS traffic to detect potential tunneling or exfiltration.
- Watchlist Monitoring: Audit activity on a default list of critical ports including FTP (21), SSH (22), RDP (3389), and SMB (445).
- Unauthorized Access Detection: Identify unexpected traffic patterns on ports that should be restricted per your security policy.
Accessing the Workbooks
These Workbooks are available as part of the NFO integration package.
- Deployment: Use the provided ARM templates to install these views into your Sentinel instance.
- Customization: All workbooks use standard KQL (Kusto Query Language) and can be easily modified to include your specific business logic or watchlists.